Enterprise-grade Remote Support and Unattended Remote Access Software
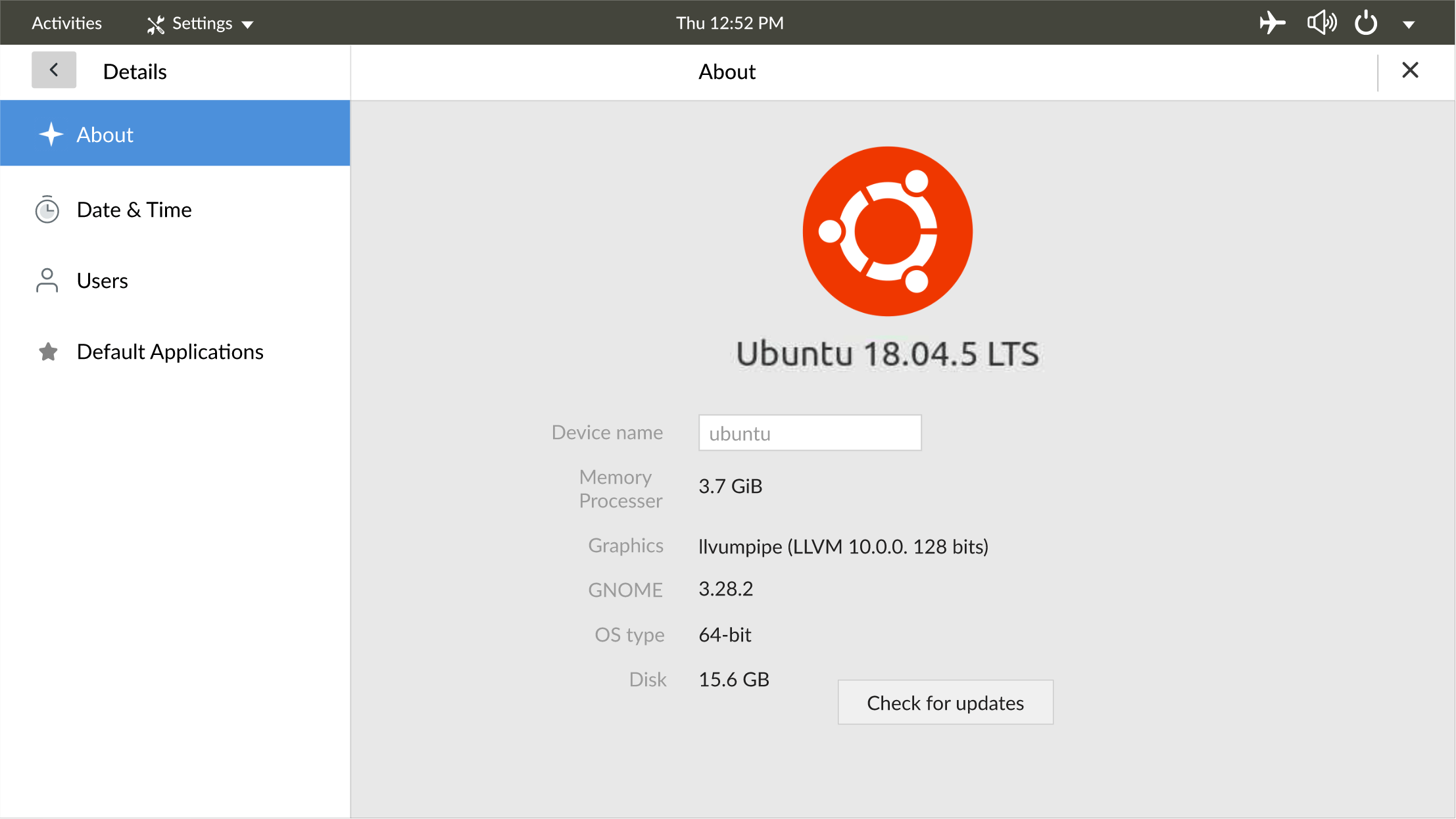
Simple Secure Feature-rich Cross Platform
Get started in 30 seconds.
- Recognized as the Customer's Choice in 2023
- Recognized as Leader for Enterprise, Fall 2023.
- Named as a Most Recommended product of 2023
Trusted by teams at

What is Zoho Assist?
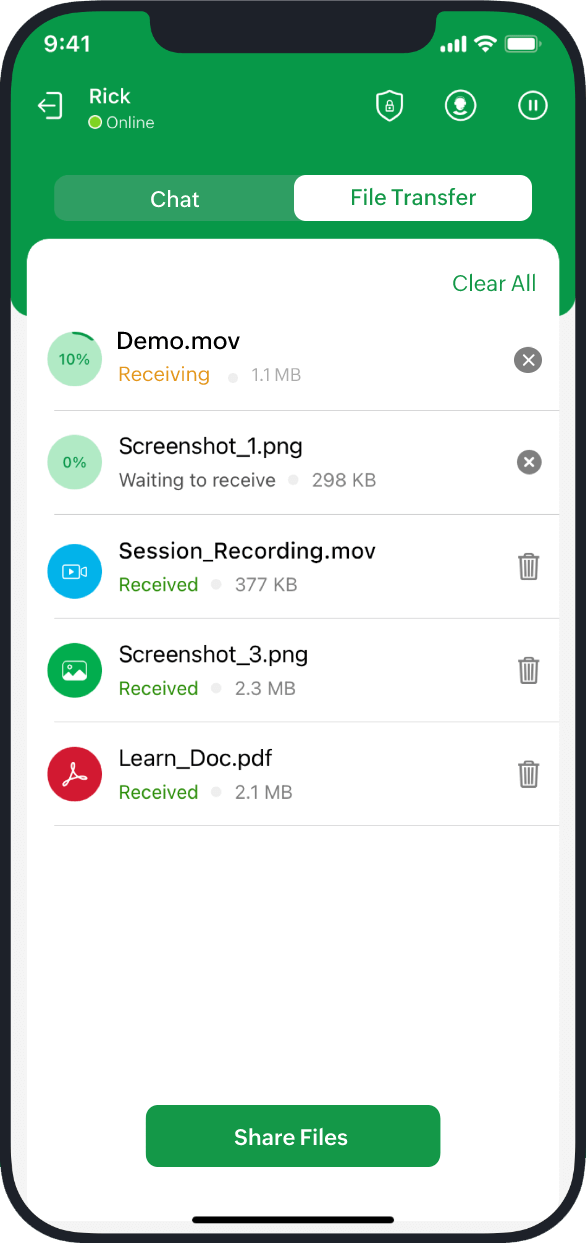
Zoho Assist empowers businesses across the globe with secure cloud-based remote support and remote access software to deliver top-notch customer support experiences. Establish secure, web-based, on-demand connections with remote PCs, laptops, mobile devices, and servers easily. Elevate your customer support experience with the industry’s best remote support solution.
Outsourced IT & MSP support
Provide attended remote support and remotely access computers anywhere in the world with ease, using our remote control software. With remote access software, you can manage remote computers efficiently and improve customer satisfaction.
Customer support
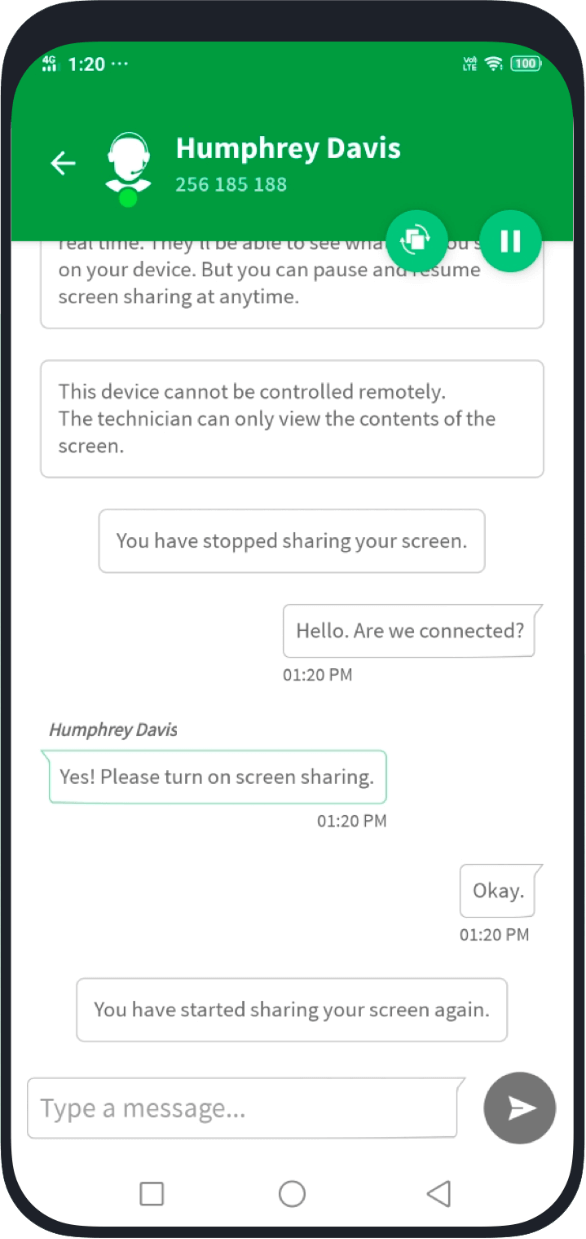
Provide attended remote desktop support to any Windows, Mac, Linux, iOS, Android, or Chromebook device. Establish remote PC access to troubleshoot faster and ensure customer satisfaction.
IT help desks
Empower your IT help desk with remote desktop support software to resolve customers’ issues. Speed up resolution time and deliver outstanding service.
850k+
Installations11M+
Remote SessionsM+
Global CustomersZoho Assist for enterprises
Our industry-leading remote access solution is easily customizable, scalable, and reliable enough to support large and growing enterprises. Consult, customize, and onboard your users with extensive solutions, enterprise features, and integrations that fulfill all your remote access requirements.
Learn more
Why use Zoho Assist?
- Enterprise-grade security: TLS 1.2 and AES 256-bit encryption
- Faster implementation and deployment
- Quick adoption and easy to use
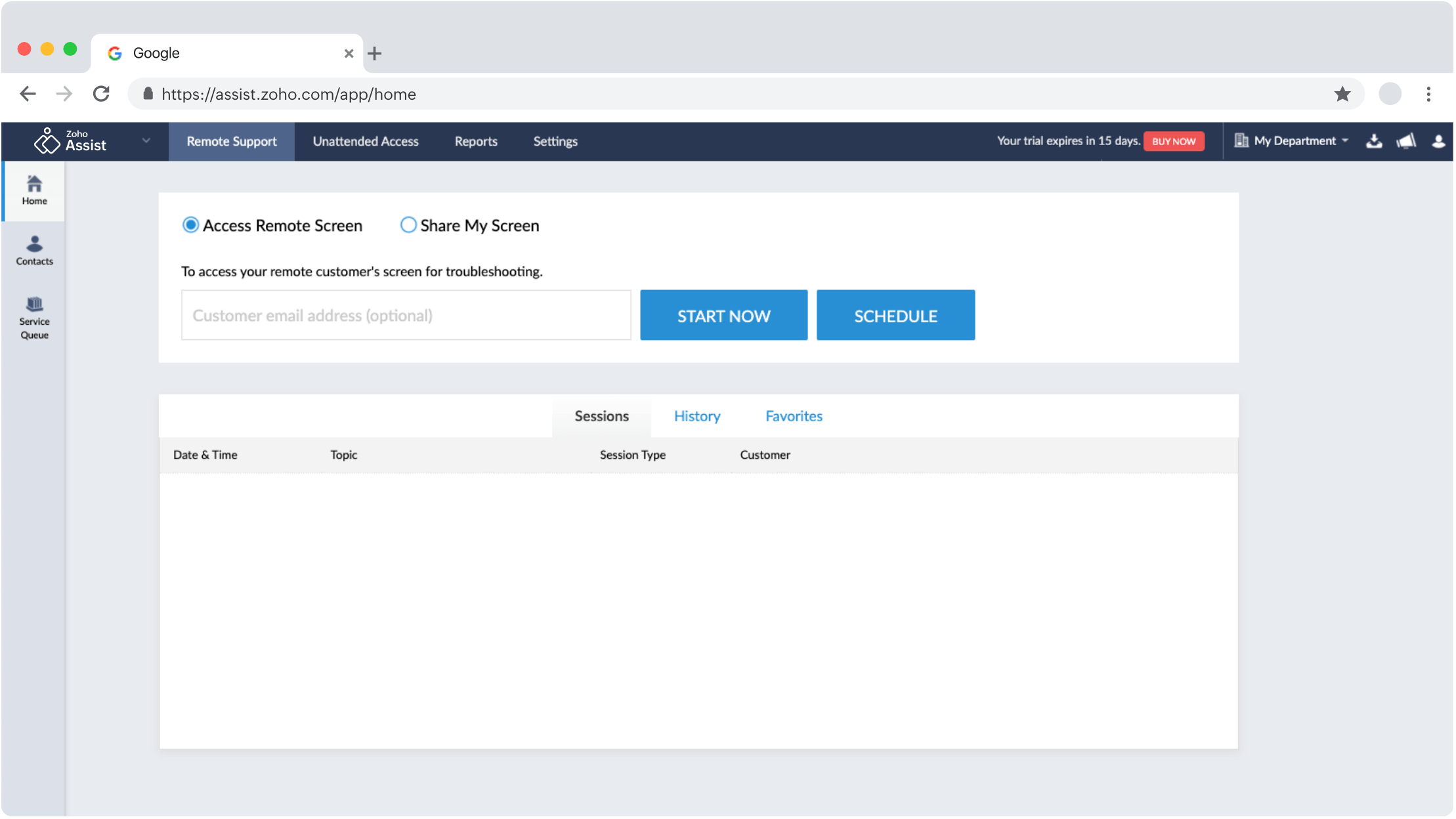
- No prior downloads needed for on-demand remote sessions
- No installation needed for technicians to start remote sessions
- Technicians can log into their accounts from any device to conduct remote sessions
- Privacy-focused remote management software
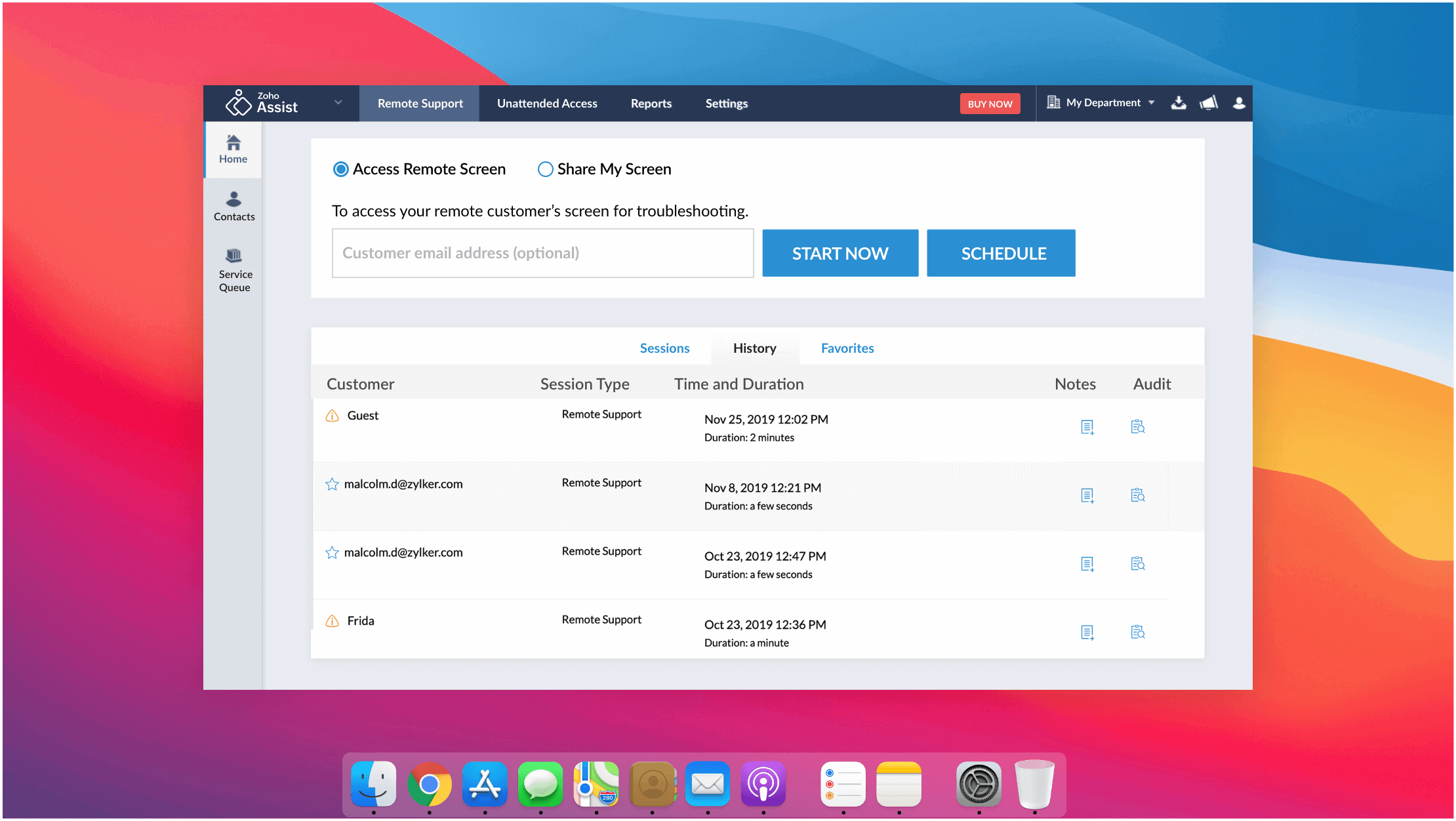
- Cross-platform support


Feature-rich remote assistance software for every scenario

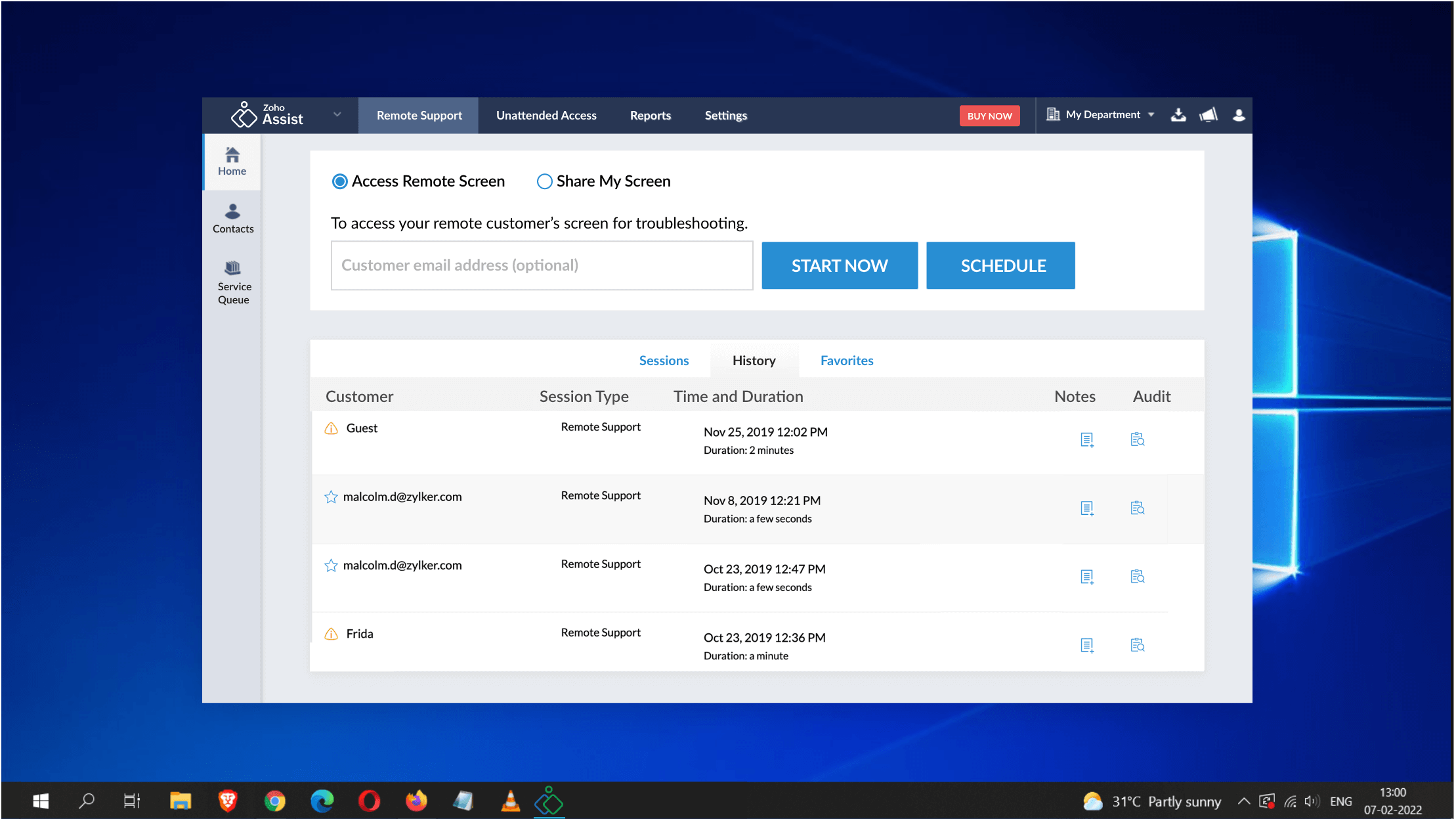
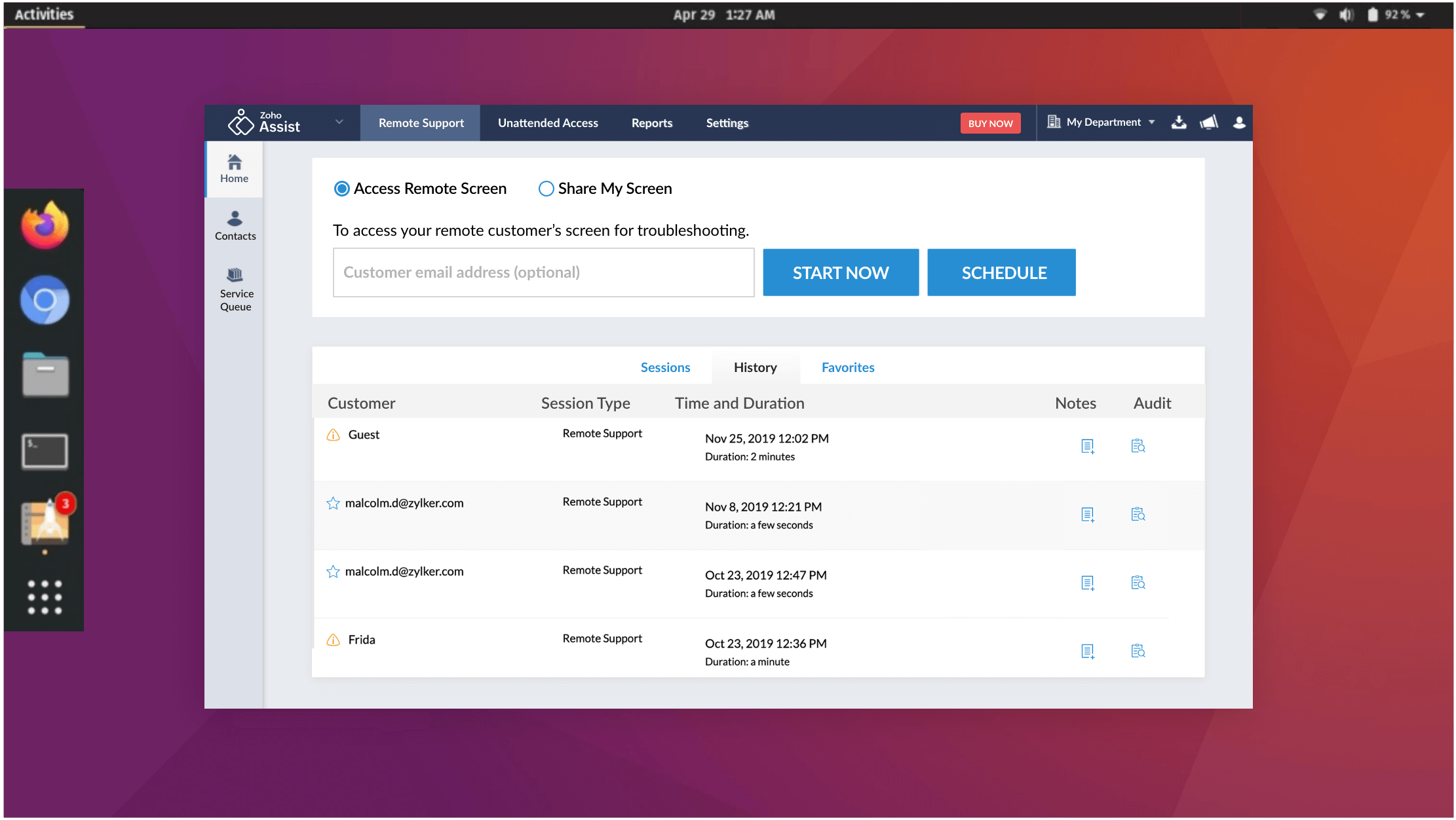
On-demand remote support
Troubleshoot a remote computer through ad-hoc or on-demand remote sessions, with no prior installation using our best-in-class remote support application. Invitees can also join a session through email invites.
Learn more
Unattended remote access
Set up unattended remote access for computers, both inside and outside LAN. Mass deployment options are also available in our remote assistance app. Assist supports both Windows and Mac.
Learn more
Online Meeting
Enhance your remote support experience with our secure online meeting and webinar software. Easily host, record, and share online meetings, broadcast video webinars, and interact with your audience using our seamless, reliable web conferencing solution.
Learn more
Augmented Reality Remote Assistance
Provide real time, augmented reality-based remote assistance by accessing your customer's smartphone camera. Troubleshoot plant machinery, servers, and more—right from your desk at any moment.
Learn more
Reboot and reconnect
Reboot any remote desktop with a single click and reconnect to the session without losing control.
Learn more
Rebranding and custom domains
Customize your Zoho Assist portal with your company logo, favicon, and email templates to match your company's branding guidelines. Customize your portal URL with custom domain mapping to carry your branding forward with our remote assistance software.
Learn moreDevice compatibility
Security at the heart of everything
Zoho is committed to the security and privacy of our customers' data. This commitment is backed by a combination of comprehensive, enterprise-grade security features, as well as rigorous, recurring audits of our applications, infrastructure, and internal policies. This ensures your data is secure and your services are uninterrupted.
Learn more

The best remote access software for Enterprise
Zoho Assist has a secure and easy-to-use interface, and is a remote support tool that has been a game changer for our organization. We highly recommend Zoho Assist to anyone looking for a secure and efficient remote support solution.

Security is paramount when dealing with remote connections in the maritime industry, and Zoho Assist’s stringent security measures give us peace of mind. We trust that our remote sessions are always secure, no matter where our ships are in the world.

Zoho Assist was a product we thought would be great for using during the pandemic. Since the pandemic, nothing has reverted to the way it was before. We now use remote assist tools daily to do system admin work.