Data Security and Privacy
Zoho Vault leverages the host-proof-hosting technique, a secure, proven mechanism which has found wide acceptance after undergoing extensive testing by security experts. Host-proof-hosting is based on the idea of hosting sensitive data in an encrypted form to ensure clients can only access and manage their data using a master password which is never transmitted to the server. The server is limited to persisting and retrieving only the encrypted data the browser forwards it, and can never actually access the sensitive data in its plain form. All encryption and decryption takes place in the client side (browser).
All passwords and other sensitive data that users store in Zoho Vault remain completely private and can only be viewed by the respective user. All user data gets encrypted and decrypted in the browser with the user's Zoho Vault master password, and only the encrypted data gets stored in Zoho's servers. The user's master password is never stored anywhere by Zoho Vault, meaning even Zoho can never access your data.
Secure Connection
As mentioned above, only encrypted data (AES-256 bit) is sent over the internet. We also mandate that all connections to our servers use Transport Layer Security (TLS 1.2/1.3) encryption with strong ciphers, for all connections.
Tested against vulnerabilities
- Zoho Vault has been comprehensively tested against cross-site scripting (XSS), SQL injection, and other vulnerabilities.
- All input data is validated
Secure sharing of passwords
Zoho Vault enables you to securely share passwords among the trusted members of your organization. The sharing process has been designed to follow the highest information security and privacy standards.
The sharing process leverages both host-proof-hosting and RSA encryption. RSA public and private keys are generated for each user of your organization. The organization administrator and users "shake hands" in a one-time process to initiate the sharing process. During that handshake, the keys are shared between the administrator and users. The entire process happens in the background, without the need for any manual action. You can find details of the entire process below, if you're interested in the technical aspect.
Step 1
When the org administrator signs up with Zoho Vault, an RSA Public-Private key pair is generated for them, along with an Org Key. This Org Key is an AES 256-bit key unique to every organization. The org admin's Private Key is encrypted using their master password and stored in Zoho Vault's database. Similarly, the Org Key is also encrypted using the org admin's RSA Public Key and stored in the database. Zoho Vault only stores the encrypted keys of the org admin's Private Key and Org Key. As per the host-proof-hosting model, the org admin's master password is not stored anywhere on the server. It remains only with the org admin.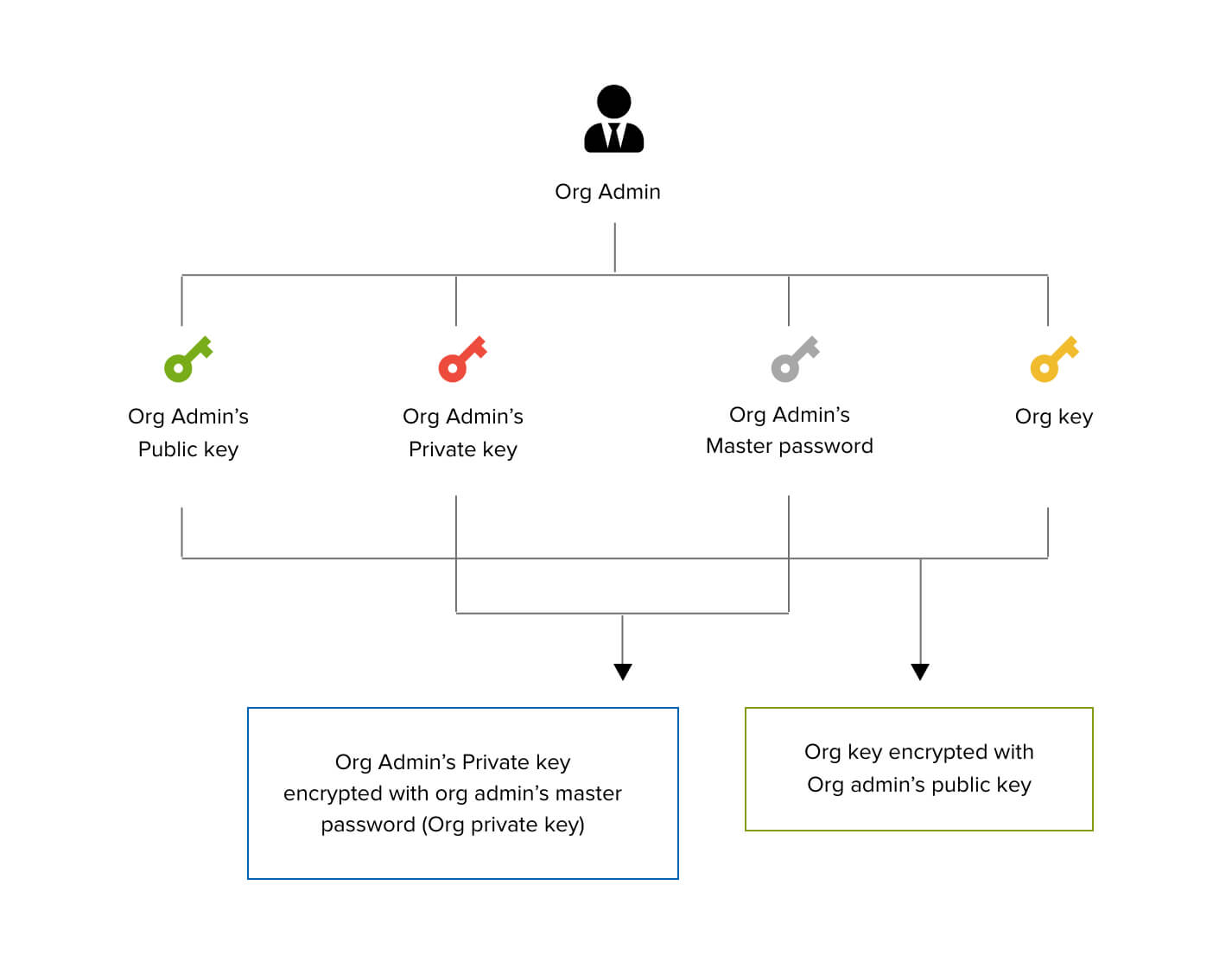
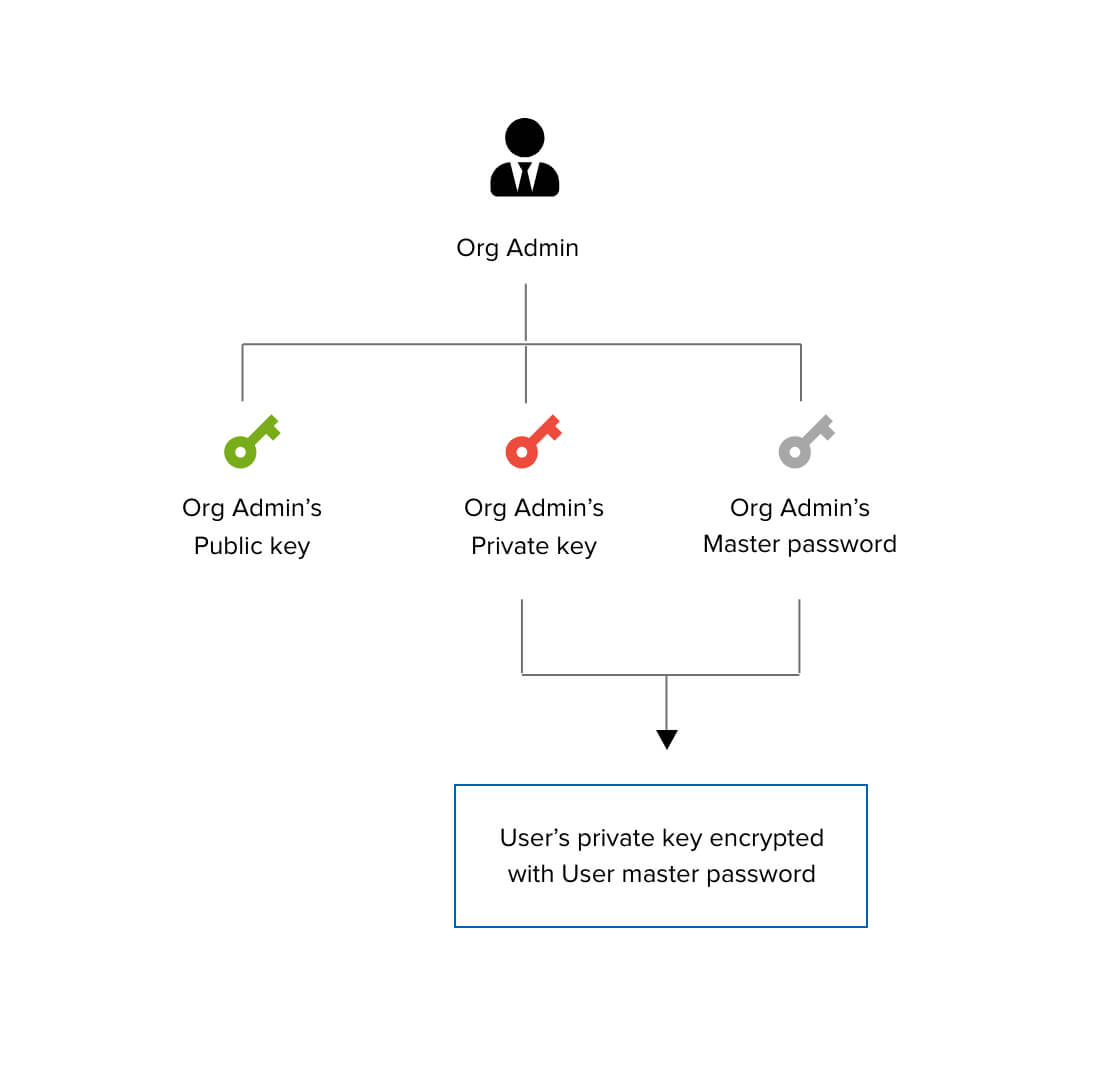
Step 2
When users in your organization sign up with Zoho Vault, an RSA Public-Private Key pair is generated for each of them. The user's private key is encrypted using their master password and stored in Zoho Vault's database.
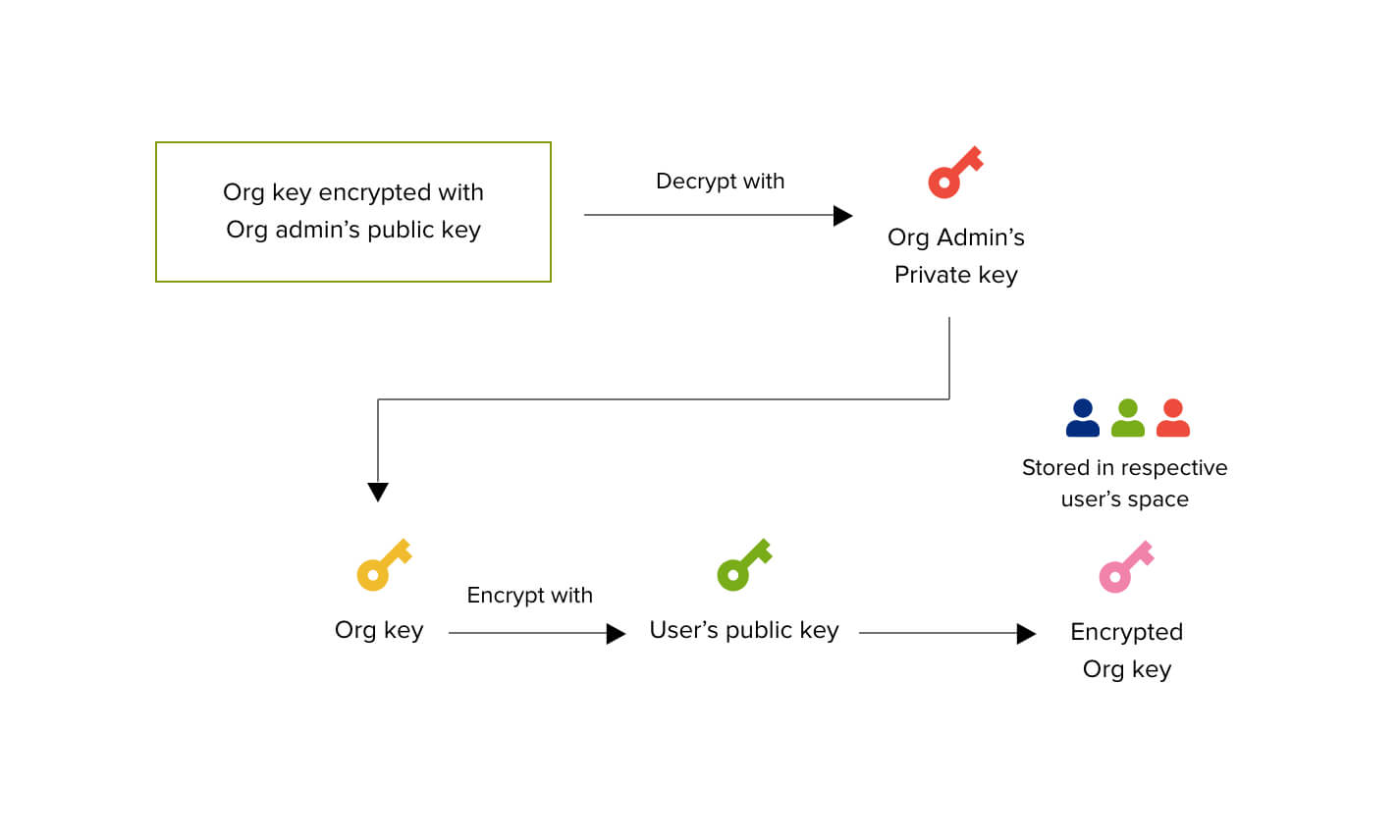
Step 3
When the org admin "shakes hands" with the org user, the encrypted Org Key stored in the database is retrieved and is decrypted using the org admin's Private Key. The Org Key is then encrypted using the user's RSA Public Key and this new encrypted Org Key is shared with the user and stored in their space in the database. This process is done for each user of Zoho Vault.
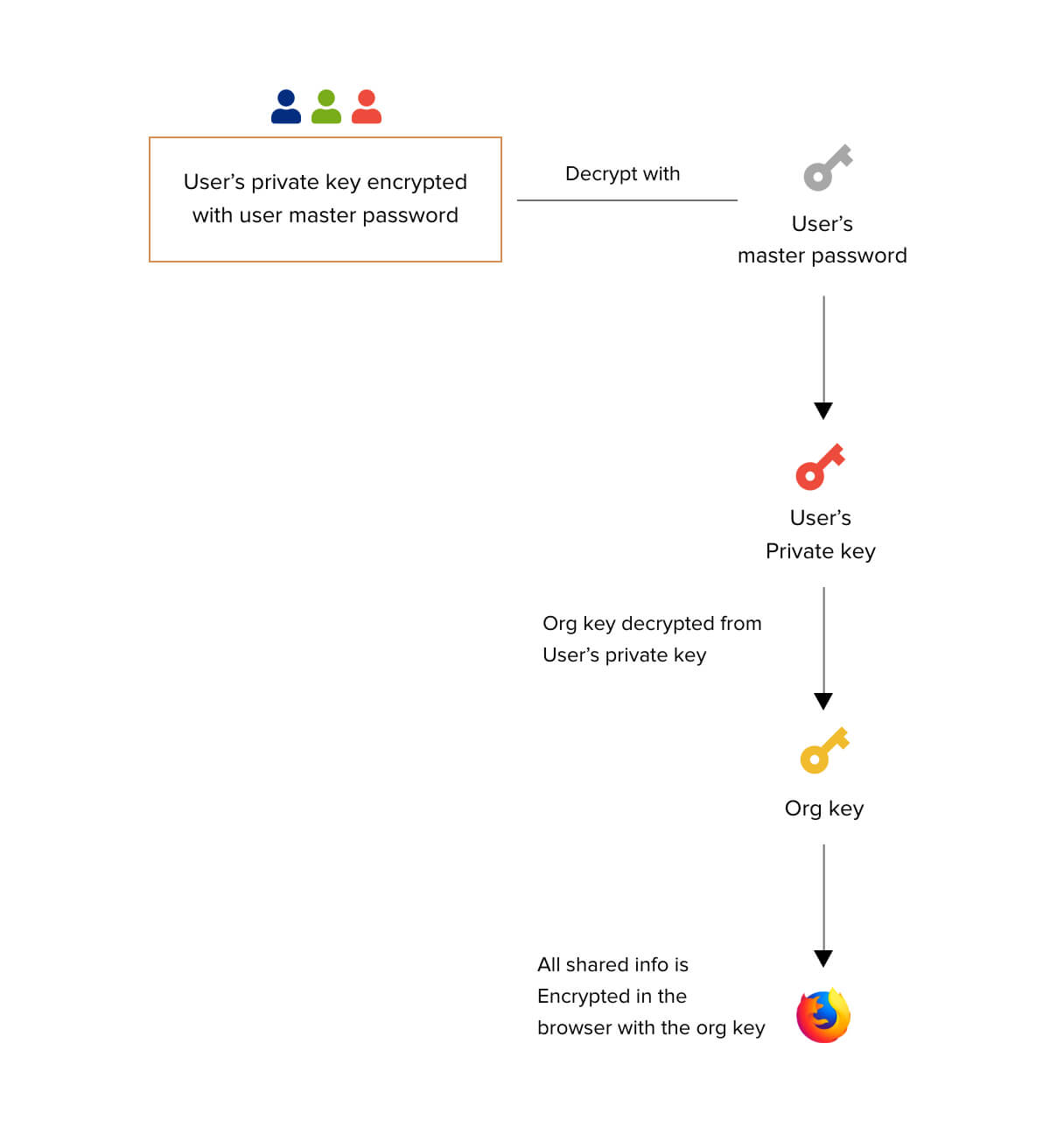
Step 4
When the user tries to share a password, the user's private key (stored in encrypted form in the database) is retrieved and decrypted using the user's master password. The encrypted Org Key that the administrator has shared with the user is then retrieved. The encrypted org key is decrypted using the user's Private Key. The password to be shared is now encrypted using the Org Key.
Password Sharing - Flow of Events
Let's use an example. Assume a user John is the admin in the organization and he wants to share one of his existing passwords with, say, five other org users, Maria, Jason, Tracy, Roger, and Amanda.
- Because the password being shared is owned by John, it is stored in Zoho Vault after being encrypted using John's master password
- When sharing is initiated, the password is decrypted using John's master password
- The password is now encrypted using the Org Key and is stored in the database
- John now shares this password with all five users. Internally, this password, which was encrypted using the Org Key is mapped to Maria, Jason, Tracy, Roger, and Amanda.
How do the users retrieve this password?
- The users decrypt their respective RSA private keys using their respective master passwords
- The users then decrypt the encrypted Org Key using their respective RSA private keys (obtained in the previous step)
- The user retrieves the password using the Org Key.
What happens when a shared password is modified?
Assume that Maria changes the shared password.
- The shared password is decrypted using the Org Key and shown
- The new password is encrypted using the Org Key and updated in the database
Important Note:
The Org Key used for encrypting and decrypting shared passwords resides in the browser when passwords are shared in the organization. It is possible for a tech-savvy user to retrieve the Org Key when they're logged in to Zoho Vault. However, this key can only be exploited when the holder gets access to Zoho Vault’s database. Since Zoho's datacenters follow state-of-the-art security protocols, this is nearly impossible. Since Zoho Vault follows the host-proof-hosting technique, it is impossible even for Zoho to access the Org Key.
Zoho's Security Policy
million users rely on Zoho's applications
With over million users accessing Zoho services worldwide, individuals and organizations count on Zoho's security and data protection to meet their needs. We take security very seriously and have developed a comprehensive set of practices, technologies, and policies to help ensure your data is secure. You can refer to Zoho's Security Policy to find in-depth details about our security strategy.
Get complete security for your passwords
Zoho Vault is a secure password management solution for businesses and individuals