What is KBA?
Knowledge-based authentication, or KBA, is an identity verification method that involves asking signers out-of-wallet questions that only they know the answers to. These questions can range from their demographic data to their purchase history or business transactions.
Why should businesses use KBA?
KBA is a legally accepted vetting process for signers based in the United States. Businesses in regulated industries, such as health care and finance amongst others, deal with sensitive data and documents that require signatures. KBA is the IRS-complaint way to authenticate signer identities.
What are the types of KBA?
Static KBA
Signers select their own pre-determined security questions and share their responses with the authenticator in advance. Example: What is your mother's maiden name?
Dynamic KBA
These security questions are generated from public and private records collected using the signer's social security number. They may range from demographic questions to questions related to credit transactions. Example: When did you purchase your property located on XYZ street?
Customer-based KBA
Companies can generate questions based on customer behavior inside their app. Example: When did you create the template "Social media policy"?
Why dynamic KBA?
Zoho Sign offers dynamic KBA because it enables senders to authenticate their signers with questions that can only be answered by them.
Security for your data
Dynamic KBA is highly secure, as it involves user-specific questions that cannot be easily answered by others. This reduces the chances of fraudulent behavior
Easy to set up
It's effortless to configure the authentication process. You can customize the number of questions and attempts according to the sensitivity of the transaction.
Popular use case
- Age restricted industries
- Banking and finance
- eCommerce
- Gaming and lottery
- Healthcare
- Insurance
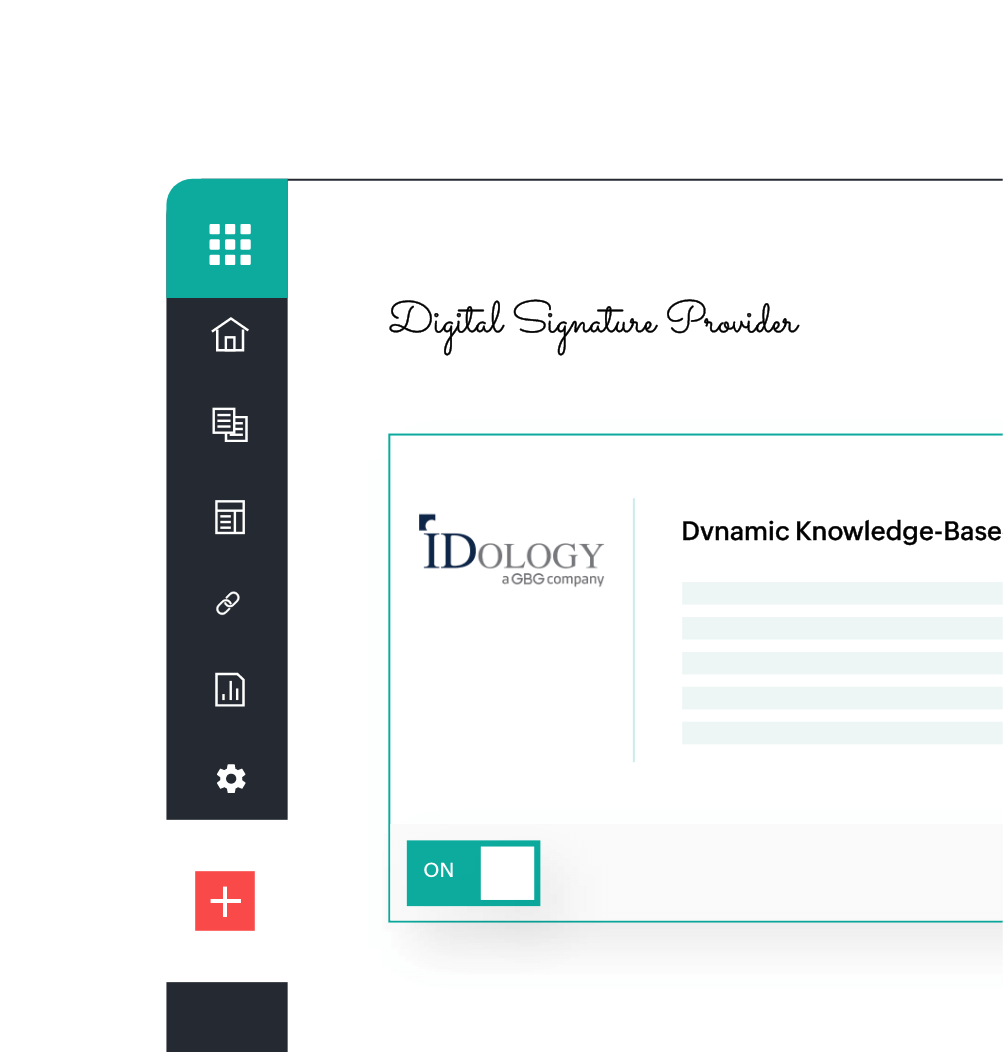
How does this integration work?
Once the integration has been enabled, senders can choose dynamic KBA as a mode of recipient authentication. Signers who receive the signing link will enter the required details to proceed to the authentication process.
Signers can access and sign the document once the authentication is completed.
Enable the integration from settings.
Configure the authentication settings.
Select dynamic knowledge based authentication as the authentication mode while adding recipient details.
Sender sends the document.
The signer recieves the document and starts the signing process.
Signer enters the required details and proceeds to the authentication process.
Signer completes the authentication process to access the document.
Signer signs the document.
FAQs
Knowledge-based authentication is a highly secure method of authenticating signers in the real world.
Zoho Sign has partnered with iDology to provide KBA.
Yes. However, the data shared to IDology is limited to your name, address, year of birth and the last four digits of your social security number (SSN).
No, Zoho Sign doesn’t store any of your data.
There are three types of KBA: static, dynamic, and customer based. Zoho Sign uses dynamic KBA powered by IDology.
Questions are generated based on the credit charges and demographic data available in public credit bureau records.
Yes, the authentication process consists of five questions that need to be answered within two minutes.
If the authentication isn't completed in the given time frame, the selected options with be auto-submitted for verification.
In such a case, you would need to contact the sender to restart the authentication process.